Asterisk Overview
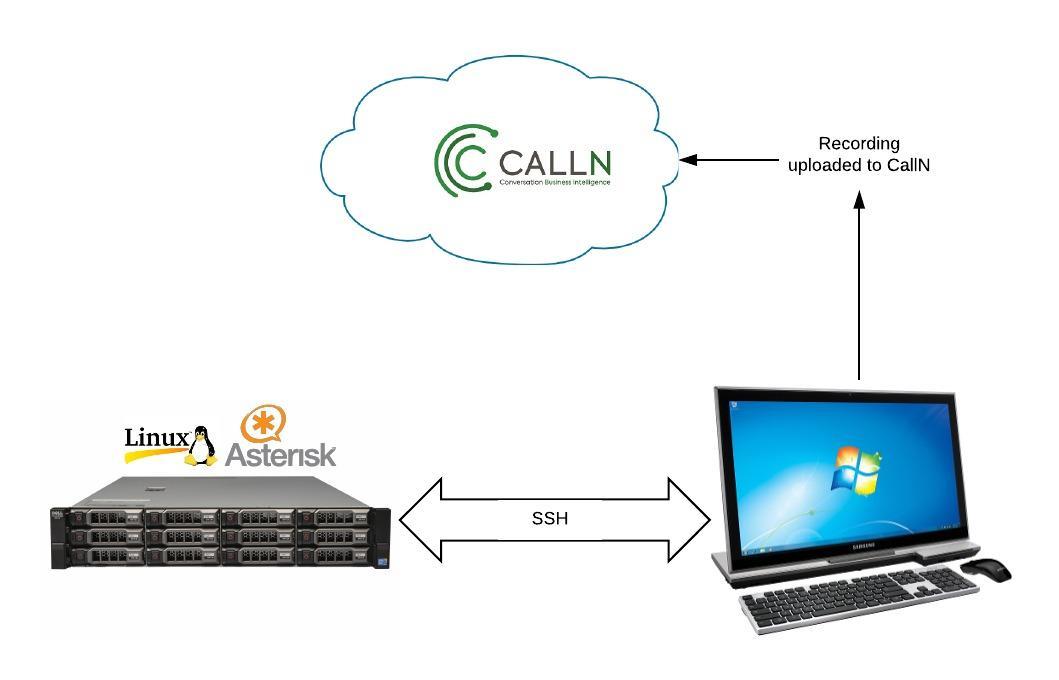
CallN can record calls direct from your Asterisk PBX. You will require a Windows computer to install the CallN client, which once configured, establishes an SSH tunnel between the Windows computer and the Linux host of the Asterisk PBX. The Linux host must have TCP Dump installed and operational for the data capture to occur. The CallN client will run a TCP Dump command to trigger the capture of the IP telephony stream, from which calls are recorded.
Installation
On the Windows computer, download and install the CallN Client. The latest CallN client can be downloaded from here.
Once the client installation has completed, you be asked to enter your CallN domain, username and password. This allows the client to log on to your CallN portal and upload recorded calls.
Open the CallN client by double clicking the icon in the system try. If the icon is not visible in the system tray, select the up arrow in the system tray to display hidden icons. Once the client is opened, select the Remote Capture tab.
Enter either the server name or IP Address if the Linux system into the Server name field.
Enter name of a user on the Linux system in to the Username field. This user will need the permissions to establish the SSH tunnel and to run TCP Dump. IT is common for people to use ‘root’ for this purpose.
In the Authentication field, either enter the password for the user specified or upload the private key which can be obtained from the Linux system.
Select ‘OK’ to save the changes.
Setting a Packet Filter
As CallN is now capturing the IP Stream direct from the Asterisk PBX, it can see calls both from the handsets and the SIP trunk connected to the PBX. This can lead to duplicate calls being recorded. If this occurs, you can set a Packet Filter to ignore traffic from one source, eliminating the duplicate call stream. It is common that the stream eliminated is the SIP trunk, and it can be done easily by entering a filter string into the packet filter. The packet filter syntax is based on standard PCAP filtering. If you know that your SIP trunk has an IP range of xxx.xxx.xxx.0/24, your filter string would be “not net xxx.xxx.xxx.0/24”. If you only have the one SIP trunk and know the IP address is xxx.xxx.xxx.xxx then the string would be “not host xxx.xxx.xxx.xxx”. All PCAP filter commands will work with CallN.
Additional information on PCAP filters can be found online. (https://www.tcpdump.org/manpages/pcap-filter.7.html)